Quantum Computing for Web Developers: What You Need to Know in 2026
Quantum computing isn’t just a physics experiment anymore. It’s headed straight for your HTTPS certificates.
McKinsey projects quantum computing revenue will grow from $4 billion in 2024 to as much as $72 billion by 2035, with chemicals, life sciences, finance, and mobility seeing the most growth (McKinsey, 2025). For web developers, the most immediate concern isn’t quantum algorithms. It’s the looming threat to the encryption that protects every API call, every user session, and every payment you process.
NIST has already set the clock: RSA and ECC will be deprecated by 2030 and completely disallowed by 2035 (NIST IR 8547, 2024). That’s not a distant future. That’s within the lifespan of code you’re writing today.
This guide covers what qubits actually are, why they threaten web security, what NIST’s new standards mean for your stack, and how to start preparing now. I’ve spent time experimenting with quantum simulators on AWS Braket and IBM Quantum to ground this in practical reality rather than hype.
TL;DR: Quantum computers will break RSA and ECC encryption, and NIST has set a 2035 deadline to migrate off these algorithms. Web developers need to understand post-quantum cryptography (ML-KEM, ML-DSA) and start auditing their cryptographic dependencies now. McKinsey projects the quantum computing market will hit $72 billion by 2035 (McKinsey, 2025).
Table of Contents
- What Is Quantum Computing?
- Why Should Web Developers Care About Quantum Computing?
- How Do Qubits Actually Work? (A Web Dev Analogy)
- What’s the Quantum Threat to Web Security?
- What Are NIST’s Post-Quantum Cryptography Standards?
- Which Quantum Algorithms Should Web Developers Know?
- What Are Quantum-as-a-Service Platforms?
- How Do You Prepare Your Stack for Post-Quantum?
- Advanced: Hybrid Classical-Quantum Applications
- Tools and Resources for Web Developers
- Getting Started
- FAQ
What Is Quantum Computing?
Quantum computing is a form of computation that uses quantum mechanical phenomena — superposition, entanglement, and interference — to process information in ways classical computers can’t. The global quantum computing market reached approximately $1.8 billion in 2025, with investors pouring nearly $2 billion into quantum startups that year, a 50% increase from 2023 (McKinsey, 2025).
Unlike classical computers that process bits as either 0 or 1, quantum computers use qubits that can represent both states simultaneously. This isn’t just a speed upgrade. It’s a fundamentally different model of computation that excels at specific problem types.
Here’s what makes quantum computing distinct:
- Superposition: A qubit exists in multiple states at once until measured
- Entanglement: Two qubits can be correlated so measuring one instantly reveals the other’s state
- Interference: Quantum algorithms amplify correct answers and cancel wrong ones
- Error sensitivity: Qubits are extremely fragile, requiring near-absolute-zero temperatures
A common misconception: quantum computers won’t replace your MacBook. They’re not universally faster. They excel at specific problem classes — factoring large numbers, searching unstructured data, and simulating molecular behavior. Your React app won’t run on a quantum chip. Neither will your PostgreSQL queries or your CI/CD pipeline.
The field has evolved rapidly since Google’s 2019 quantum supremacy claim. In 2024, Google’s Willow chip demonstrated exponential error reduction with 105 qubits. IBM plans to ship Kookaburra, a 1,386-qubit multi-chip processor, in 2026. And Microsoft unveiled Majorana 1, the world’s first topological qubit processor, in February 2025 — placing eight qubits on a chip designed to scale to a million (Microsoft, 2025).
Three hardware approaches are competing: superconducting qubits (Google, IBM), trapped ions (IonQ, Quantinuum), and topological qubits (Microsoft). Each makes different tradeoffs in qubit stability, gate speed, and scalability. Think of it like the early days of web browsers — multiple rendering engines competing, all converging toward the same capability.
For web developers, the hardware race matters less than the outcome: when any approach produces enough logical qubits, your encryption breaks. And with Q1 2025 seeing $1.25 billion in quantum investment — a 128% year-over-year surge — that timeline is accelerating (SpinQ, 2025).
computing fundamentals
Why Should Web Developers Care About Quantum Computing?
The single most compelling reason: quantum computers will eventually break the encryption your entire web stack depends on. Gartner predicts that by 2029, advances in quantum computing will make most conventional asymmetric cryptography unsafe to use (Gartner, 2026). Every HTTPS connection, JWT token, and OAuth flow you build relies on RSA or ECC — both of which are quantum-vulnerable.
The quantum computing market is growing at a 32-41% CAGR, depending on which research firm you ask. But market size isn’t why you should care. Here’s what matters for your daily work.
The encryption clock is ticking. NIST will deprecate RSA and ECC by 2030 and fully disallow them by 2035 (NIST IR 8547, 2024). If your app processes health data, financial records, or anything with a long confidentiality window, the migration timeline starts now.
“Harvest now, decrypt later” is already happening. State-sponsored adversaries are collecting encrypted traffic today, planning to decrypt it once quantum computers arrive. If your API transmits data that needs to stay confidential for 10+ years — medical records, financial transactions, legal communications — it’s already at risk. The data doesn’t need to be valuable now. It needs to be valuable when quantum decryption arrives.
The migration won’t be quick. The industry’s shift from SHA-1 to SHA-2 took over 12 years. Post-quantum migration is more complex because it touches key exchange, digital signatures, and certificate infrastructure simultaneously. According to Bain & Company, it takes three to four years on average just to go from awareness to a structured PQC approach (Bain & Company, 2025). That means organizations starting in 2026 won’t be fully migrated until 2029 or 2030 at the earliest.
What happens if you ignore this? Your TLS certificates become worthless. Your stored encrypted data becomes readable. Your payment processing fails compliance audits. And if you’re building apps in regulated industries — healthcare, finance, government — you’ll face legal liability for data exposed through deprecated encryption.
This isn’t theoretical. The UK’s National Cyber Security Centre (NCSC) has published its own 2035 PQC migration deadline alongside NIST, creating coordinated international pressure that no global web application can sidestep.
Even if general-purpose quantum computing stalls for another decade, the cryptographic migration is happening regardless. NIST’s standards are finalized. Browser vendors are shipping PQC support. Cloudflare already protects over 50% of its human web traffic with post-quantum encryption (Cloudflare, 2025). The web security landscape is shifting whether or not a quantum computer ever touches your code.
Citation Capsule: Quantum computing threatens all asymmetric encryption used in web development. NIST will deprecate RSA and ECC by 2030 and disallow them by 2035 (NIST IR 8547, 2024). Web developers should begin auditing cryptographic dependencies now, as the SHA-1 to SHA-2 migration took over 12 years.
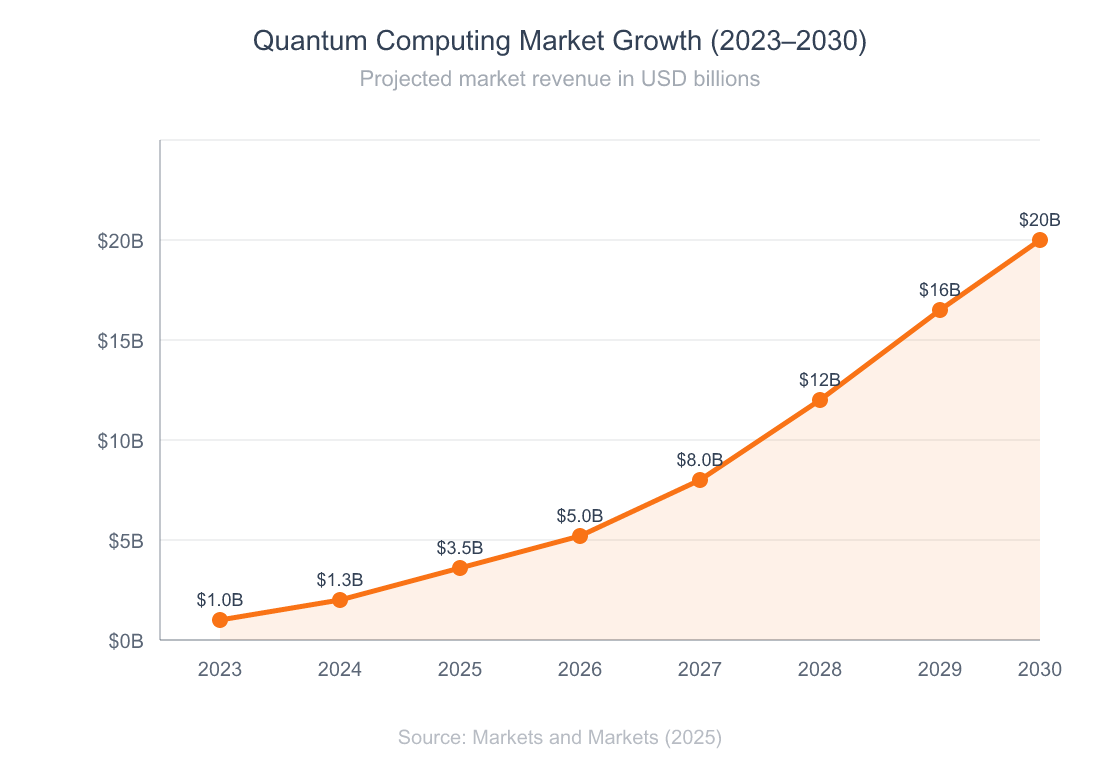
The quantum computing market is projected to grow from $1 billion in 2023 to over $20 billion by 2030, driven by hardware advances and cloud accessibility.
future of developer careers
How Do Qubits Actually Work? (A Web Dev Analogy)
A qubit is the fundamental unit of quantum information, analogous to a classical bit but capable of existing in a superposition of both 0 and 1 simultaneously. Google’s 105-qubit Willow chip completed a calculation in five minutes that would take a classical supercomputer 10^25 years — demonstrating why even modest qubit counts can outperform classical machines for specific tasks (Google AI Blog, 2024).
If you’re a web developer, think of it this way.
Classical Bits vs. Qubits: The API Analogy
A classical bit is like a boolean variable: true or false. A qubit is more like a Promise in JavaScript. Before it resolves (before you measure it), it exists in a pending state that represents both outcomes with different probabilities. Once you observe it, it collapses to one definite value.
But here’s where the analogy gets interesting. Entanglement is like a WebSocket connection between two qubits. Change one, and the other responds instantly — no HTTP round trip required. Superposition lets a quantum computer evaluate multiple paths simultaneously, like running every branch of an if/else tree at once. Interference is the trick that makes it useful: it amplifies correct answers and cancels wrong ones, like a filter that eliminates bad routes in a pathfinding algorithm.
The combination of these three properties is what gives quantum computers their power on specific problem types. It’s not that they’re faster at everything. They’re fundamentally better at problems with a particular mathematical structure.
Why Qubit Count Alone Is Misleading
You’ll see headlines about 1,000-qubit machines. Don’t take that at face value. What matters is the error rate and whether qubits are logical (error-corrected) or physical (raw, noisy).
IBM’s Kookaburra processor, shipping in 2026, will have 1,386 physical qubits. But you might only get a handful of usable logical qubits from those. Microsoft’s topological approach with Majorana 1 aims to solve this by building qubits that are inherently more stable — small enough to fit a million on a chip the size of a graham cracker (Microsoft, 2025).
The takeaway for web developers: don’t get distracted by qubit counts. Focus on what these machines can break and what tools you’ll need when they do.
What’s the Quantum Threat to Web Security?
Quantum computers will break RSA and ECC, the two encryption algorithms that protect virtually all web traffic. Current analysis suggests RSA-2048 could be broken with roughly 1,000-1,400 logical qubits running for about a week — far fewer than previously assumed (Post-Quantum, 2025). Based on current progress, a 2032 Q-Day estimate appears realistic even without further breakthroughs.
Here’s what’s at stake for your web applications.
What Breaks and When?
TLS/HTTPS: Every secure connection uses RSA or ECC for the handshake. When Shor’s algorithm runs on a sufficiently powerful quantum computer, an attacker can derive private keys from public keys. Your HTTPS is just HTTP.
Digital certificates: The certificates that prove your server is who it says it is rely on RSA or ECC signatures. Quantum computers invalidate those signatures.
JWTs and OAuth: If you sign tokens with RSA (RS256) or ECC (ES256), those signatures become forgeable.
Stored encrypted data: Anything encrypted with RSA today can be decrypted later. This “harvest now, decrypt later” (HNDL) threat is why the timeline matters even before Q-Day arrives.
WebSocket connections: If your real-time features use WSS (WebSocket Secure), the underlying TLS handshake faces the same quantum vulnerability. Chat applications, live dashboards, collaborative editing tools — all of these depend on quantum-vulnerable key exchange.
SSH and deployment pipelines: Your CI/CD pipeline, server access, and Git operations over SSH all use RSA or ECDSA keys. A compromised deployment pipeline is a compromised application.
The Y2Q Timeline
“Y2Q” — Years to Quantum — marks when quantum computers can break current encryption. Here’s the realistic timeline:
- Now: HNDL attacks are collecting encrypted data for future decryption
- 2029: Gartner predicts most asymmetric cryptography becomes unsafe
- 2030: NIST deprecates RSA, ECDSA, EdDSA, DH, and ECDH
- 2032: Plausible Q-Day based on current hardware trajectories
- 2035: NIST fully disallows legacy quantum-vulnerable algorithms
How confident are experts? Citi’s January 2026 report called it “The Trillion-Dollar Security Race,” framing quantum threats as an urgent financial risk for every industry handling encrypted data (Citi, 2026).
Citation Capsule: The quantum threat to web security is already active through “harvest now, decrypt later” attacks. RSA-2048 could fall to approximately 1,000-1,400 logical qubits running for a week (Post-Quantum, 2025), and NIST will fully disallow these algorithms by 2035. Web developers who handle long-lived confidential data should treat PQC migration as urgent.
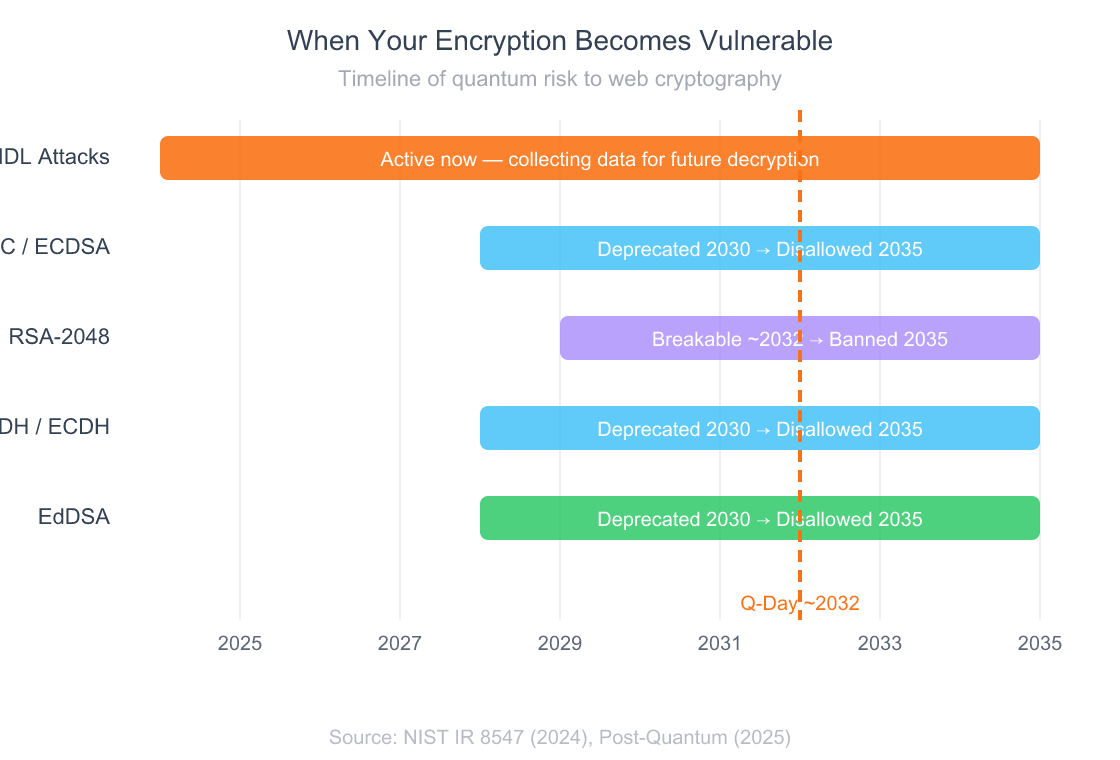
Every asymmetric encryption algorithm used in web development faces deprecation by 2030 and full removal by 2035 under NIST’s transition plan.
What Are NIST’s Post-Quantum Cryptography Standards?
NIST released three finalized post-quantum cryptography standards in August 2024, providing web developers with concrete algorithms to replace RSA and ECC (NIST, 2024). These aren’t theoretical proposals. They’re production-ready standards that browser vendors and TLS libraries are already implementing.
Here’s what each standard does and why it matters for your code.
ML-KEM (FIPS 203) — Key Encapsulation
ML-KEM (Module-Lattice-Based Key-Encapsulation Mechanism) replaces RSA and ECDH for key exchange. When your browser opens an HTTPS connection, ML-KEM will handle the handshake instead of RSA key exchange. It’s based on CRYSTALS-Kyber and produces comparatively small encryption keys with fast operation.
Cloudflare has already deployed a hybrid approach — combining ML-KEM with classical X25519 — protecting over 50% of human web traffic through their network with post-quantum encryption as of October 2025 (Cloudflare, 2025).
ML-DSA (FIPS 204) — Digital Signatures
ML-DSA (Module-Lattice-Based Digital Signature Algorithm) replaces RSA and ECDSA for signatures. This covers TLS certificates, code signing, and JWT tokens. It’s based on CRYSTALS-Dilithium.
SLH-DSA (FIPS 205) — Backup Signatures
SLH-DSA (Stateless Hash-Based Digital Signature Algorithm) is a backup digital signature standard using a different mathematical approach. If lattice-based cryptography (ML-DSA) proves vulnerable, SLH-DSA provides a fallback. It uses hash functions that are well-understood and trusted.
What’s Still Coming
A fourth algorithm, FN-DSA (based on Falcon), and a fifth, HQC (for key encapsulation), are still being standardized. The HQC draft standard is expected in early 2026 with final publication in 2027.
What Changes in Practice for Web Developers?
Your TLS libraries, certificate authorities, and browser APIs will gradually swap out RSA/ECC for these algorithms. You won’t rewrite encryption from scratch. But you will need to update dependencies, test compatibility, and verify your deployment pipeline handles the larger key sizes these standards produce.
The key size difference is worth noting. ML-KEM public keys run about 1,568 bytes versus 32 bytes for X25519. ML-DSA signatures are around 2,420 bytes versus 256 bytes for ECDSA. This means larger TLS handshakes and increased bandwidth.
For most web apps, the performance impact will be minimal — Cloudflare’s deployment showed negligible latency increases. But if you’re processing thousands of TLS handshakes per second, benchmark early. The first post-quantum TLS certificates are expected in 2026, with broad availability in 2027. In February 2026, Cloudflare became the first SASE platform to support PQC across all major configurations (Cloudflare, 2026).
Citation Capsule: NIST finalized three post-quantum cryptography standards in 2024: ML-KEM (FIPS 203) for key exchange, ML-DSA (FIPS 204) for digital signatures, and SLH-DSA (FIPS 205) as a backup signature scheme (NIST, 2024). Cloudflare already protects 50%+ of its human web traffic using hybrid post-quantum key exchange.
payment security implications
Which Quantum Algorithms Should Web Developers Know?
Two quantum algorithms have direct implications for web development: Shor’s algorithm threatens your encryption, and Grover’s algorithm weakens your hashing. Understanding what they do — not how to build them — is what matters for your threat model.
Shor’s Algorithm: The Encryption Killer
Shor’s algorithm efficiently factors large numbers and computes discrete logarithms. This is the algorithm that breaks RSA (which depends on factoring being hard) and ECC (which depends on the discrete log problem being hard). A sufficiently powerful quantum computer running Shor’s algorithm could derive your private key from your public key.
What does “sufficiently powerful” mean? Current estimates suggest roughly 1,000-1,400 logical qubits running for about a week could crack RSA-2048, using modern error-correction techniques like “magic state cultivation” (Post-Quantum, 2025). That’s far less than the 20 million physical qubits researchers once assumed were necessary. Today’s machines aren’t there yet. But the trajectory is clear, and the gap is shrinking faster than expected.
Grover’s Algorithm: The Hashing Weakener
Grover’s algorithm provides a quadratic speedup for searching unsorted databases. For web developers, this means symmetric encryption (AES) and hashing (SHA-256) lose half their effective security bits. AES-128 drops to 64-bit security. AES-256 drops to 128-bit security — which is still considered safe.
What this means practically: if you’re using AES-256 and SHA-256, you’re mostly fine against quantum attacks. The threat is primarily to asymmetric cryptography. But if any part of your system still uses AES-128 or MD5, treat the quantum timeline as your upgrade deadline.
Are there quantum algorithms that could help web development? Potentially. Quantum machine learning, quantum optimization, and quantum simulation are all active research areas. But here’s the honest assessment: none of these will affect your day-to-day work for years. The cryptographic threat is the one demanding action now.
What Are Quantum-as-a-Service Platforms?
Quantum-as-a-Service (QaaS) platforms let developers experiment with quantum computing through cloud APIs without owning quantum hardware. Over $36 billion in public and private investment has flowed into quantum technology, with 70+ startups building quantum software and tooling (The Quantum Insider, 2025). The three major cloud providers all offer quantum services.
AWS Braket
Amazon Braket provides access to multiple quantum hardware types: superconducting qubits (Rigetti), trapped ions (IonQ), and quantum annealers (D-Wave). In February 2025, AWS unveiled Ocelot, its first proprietary quantum chip built with cat qubits that suppress noise. Pay-per-task pricing with free-tier simulators. Python SDK integrates with the broader AWS ecosystem.
Azure Quantum
Microsoft’s platform integrates Quantinuum and IonQ hardware into Azure. In 2025, Microsoft and Quantinuum achieved high-fidelity entanglement of 12 logical qubits — a significant milestone. Azure Quantum emphasizes hybrid classical-quantum workflows, making it natural for enterprise teams already on Azure. Credits-based pricing with free tier. Python and Q# SDKs.
Google Quantum AI
Google leads on research with the Willow chip’s quantum advantage demonstration. Provides simulators and quantum backends via API, focused on AI-quantum convergence. Access is primarily research-oriented. Cirq (Python) SDK. If you’re interested in quantum ML, this is the platform to watch.
I’ve run simple quantum circuits on AWS Braket’s simulator and IonQ’s trapped-ion hardware. The experience feels like writing any other cloud function — you define a circuit, submit it, and get results back. The learning curve isn’t in the cloud tooling. It’s in understanding what quantum circuits actually compute. If you can use an AWS SDK, you can use Braket. The quantum concepts are the hard part.
Citation Capsule: All three major cloud providers now offer Quantum-as-a-Service: AWS Braket, Azure Quantum, and Google Quantum AI. Over $36 billion has been invested in quantum technology globally, with Q1 2025 alone attracting $1.25 billion — a 128% year-over-year surge in quantum computing investment (SpinQ, 2025).
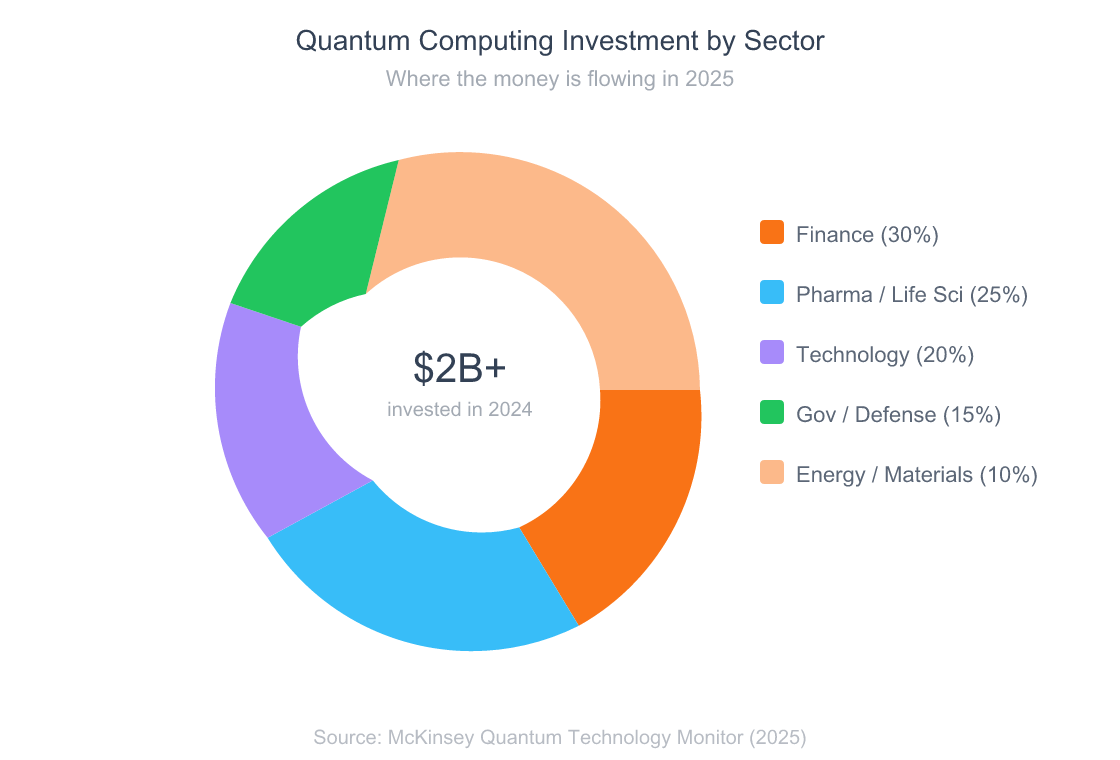
Financial services leads quantum computing investment at 30%, followed by pharmaceuticals and life sciences — both sectors with massive optimization and simulation needs.
How Do You Prepare Your Stack for Post-Quantum?
The migration to post-quantum cryptography isn’t optional — NIST has set hard deadlines. Cloudflare’s automatic SSL/TLS rollout will enable post-quantum handshakes with all origins by June 2026 (Cloudflare, 2026). The first post-quantum certificates are expected in 2026, though they won’t be broadly enabled by default until 2027.
Here’s a practical checklist for web developers. You don’t need to become a cryptographer. You need to audit, update, and test.
Step 1: Audit Your Cryptographic Dependencies
Run an inventory of every place your application uses cryptography:
- TLS certificates: What algorithm signs them? (likely RSA or ECDSA)
- JWT signing: Are you using RS256 or ES256? Both are quantum-vulnerable
- API authentication: OAuth tokens, webhook signatures, API keys
- Database encryption: At-rest encryption algorithms
- Third-party services: Payment gateways, auth providers, CDN configurations
Most developers don’t realize how many layers of cryptography exist in a typical web app. Every npm package that calls crypto is a potential migration point. Run npm ls and check which packages depend on cryptographic primitives. You’ll likely find more than you expected.
For a typical Node.js web application, you might find cryptographic dependencies in your auth library, session management, cookie signing, CSRF tokens, webhook verification, and database connection strings. Each one is a migration target.
Step 2: Update Your Libraries
OpenSSL 3.x already includes experimental post-quantum support. The liboqs (Open Quantum Safe) library provides implementations of ML-KEM and ML-DSA for most languages. Check whether your framework’s TLS library supports hybrid key exchange.
Step 3: Test Hybrid Mode
The industry consensus is to use hybrid cryptography during the transition — combining classical algorithms with post-quantum ones. If either algorithm breaks, the other still protects you. Cloudflare’s approach (ML-KEM + X25519) is the model to follow.
Step 4: Watch Your Key Sizes
Post-quantum keys are significantly larger than RSA/ECC keys. ML-KEM public keys are around 1,568 bytes versus 32 bytes for X25519. This affects bandwidth, handshake times, and storage. Test your application’s performance with larger keys before deploying.
Step 5: Plan for Certificate Rotation
When PQC certificates become available, you’ll need to rotate. If you’re using automated certificate management (Let’s Encrypt, Certbot), updates should propagate automatically. If you manage certificates manually, this is your reminder to automate.
Common mistake: assuming your cloud provider handles everything. They’ll update their infrastructure, but your application-level cryptography — JWTs, webhook signatures, encrypted database fields — is your responsibility.
What About Third-Party Dependencies?
Your own code is just one layer. Audit every third-party service that handles encrypted data on your behalf. Payment processors, authentication providers (Auth0, Firebase Auth, Clerk), email services, and CDNs all have their own cryptographic stacks. Ask them about their PQC migration timeline.
If you’re building a SaaS product, your customers will eventually ask about your post-quantum readiness. Having an answer — even “we’ve audited and have a migration plan” — puts you ahead of most competitors. The quantum computing in healthcare market grew from $167 million in 2025 to $231 million in 2026, signaling how seriously regulated industries take this threat (Towards Healthcare, 2026).
database encryption practices
Advanced: Hybrid Classical-Quantum Applications
If you’re already comfortable with the security implications and want to explore quantum computing’s potential, hybrid classical-quantum applications represent the near-term opportunity.
What Hybrid Means in Practice
A hybrid application runs most of its workload on classical infrastructure and delegates specific subproblems to a quantum processor. Think of it like calling an external API — your Node.js server sends a quantum circuit to AWS Braket, gets results back, and processes them classically.
Current use cases furthest along include optimization problems (route planning, portfolio balancing), molecular simulation (drug discovery — Google simulated Cytochrome P450 with Boehringer Ingelheim), and quantum random number generation for cryptographic key generation.
When to Consider Quantum
Don’t use quantum computing because it sounds interesting. Use it when your problem has a specific characteristic: combinatorial explosion, exponential search spaces, or molecular-level simulation. If your problem can be solved with a SQL query or a well-tuned algorithm, classical computing wins every time.
Here’s a practical filter. Ask yourself: does my problem’s difficulty grow exponentially with input size? Does it require simulating quantum systems? Does it involve optimization over millions of configurations? If the answer is no to all three, stick with classical computing. The real-world quantum applications are landing first in drug simulation, protein folding, and molecular modeling — domains far from typical web development. If your web app doesn’t need to simulate molecular interactions or optimize portfolios across millions of variables, quantum computing won’t speed up your code. Focus your quantum energy on the security migration instead.
The developers who’ll benefit most from quantum computing aren’t those building quantum algorithms from scratch. They’re full-stack engineers who can identify optimization bottlenecks in classical systems and know enough about quantum circuits to delegate those bottlenecks to a QaaS platform. Quantum computing is becoming an API call, not a career change.
Testing quantum circuits on AWS Braket taught me that the biggest limitation isn’t the quantum hardware — it’s formulating problems in a way quantum computers can solve. Most web development problems aren’t quantum-suitable. But the exercise of thinking in terms of quantum gates changed how I approach optimization problems classically.
Tools and Resources for Web Developers
AWS Braket and IBM Quantum are the two most accessible starting points for web developers exploring quantum computing. Both offer free tiers, Python SDKs, and extensive documentation.
QaaS Platforms
- AWS Braket: Multi-hardware access, pay-per-task. Best for AWS teams.
- IBM Quantum: Free real hardware access, Qiskit framework. Best for learning.
- Azure Quantum: Hybrid workflows, Q# language. Best for Azure shops.
PQC Libraries
- liboqs (Open Quantum Safe): Reference PQC algorithm implementations. Free, open source.
- OpenSSL 3.x: Experimental PQC provider support. Free.
- Cloudflare PQC docs: Practical hybrid PQC deployment guidance. Free.
Learning Resources
- IBM Quantum Learning: Structured courses with interactive circuit builder. Free.
- Qiskit Textbook: Open source quantum computing textbook. Free.
- NIST PQC Standards: Official standard documentation. Free.
I’ve found IBM Quantum Learning to be the most developer-friendly resource. The interactive circuit builder removes the math barrier and lets you visualize qubit states in real time. If you can write a function, you can build a quantum circuit — even if you don’t fully understand the linear algebra behind it. Start there, then graduate to Qiskit notebooks when you want to experiment on actual hardware.
Getting Started
Start by running a cryptographic audit of your current web application this week. You don’t need to understand quantum physics. You need to know where RSA and ECC live in your codebase.
Step 1 (This week): Use grep -r "RS256\|ES256\|RSA\|ECDSA" your-project/ to find every place your application references quantum-vulnerable algorithms. Check your package.json or requirements.txt for cryptography libraries.
Step 2 (This month): Sign up for IBM Quantum (free) and complete their “Basics of Quantum Information” course. It takes about four hours and gives you enough context to evaluate quantum claims critically. Run a simple circuit on real hardware.
Step 3 (This quarter): Test hybrid PQC in a staging environment. If you use Cloudflare, enable post-quantum key exchange on your domain. If you manage your own TLS, experiment with liboqs. Document what breaks and what works.
The learning curve is real, but the tools are more accessible than you’d expect. If you’ve ever configured TLS certificates or debugged an SSL handshake, you have the technical background to start the PQC transition. The migration isn’t glamorous. But it’s the kind of quiet, methodical preparation that separates secure applications from compromised ones when the quantum threat materializes.
Most web developers won’t become quantum engineers. But every web developer will need to understand the cryptographic shift. The good news: this is an infrastructure migration, not a paradigm shift in how you build apps.
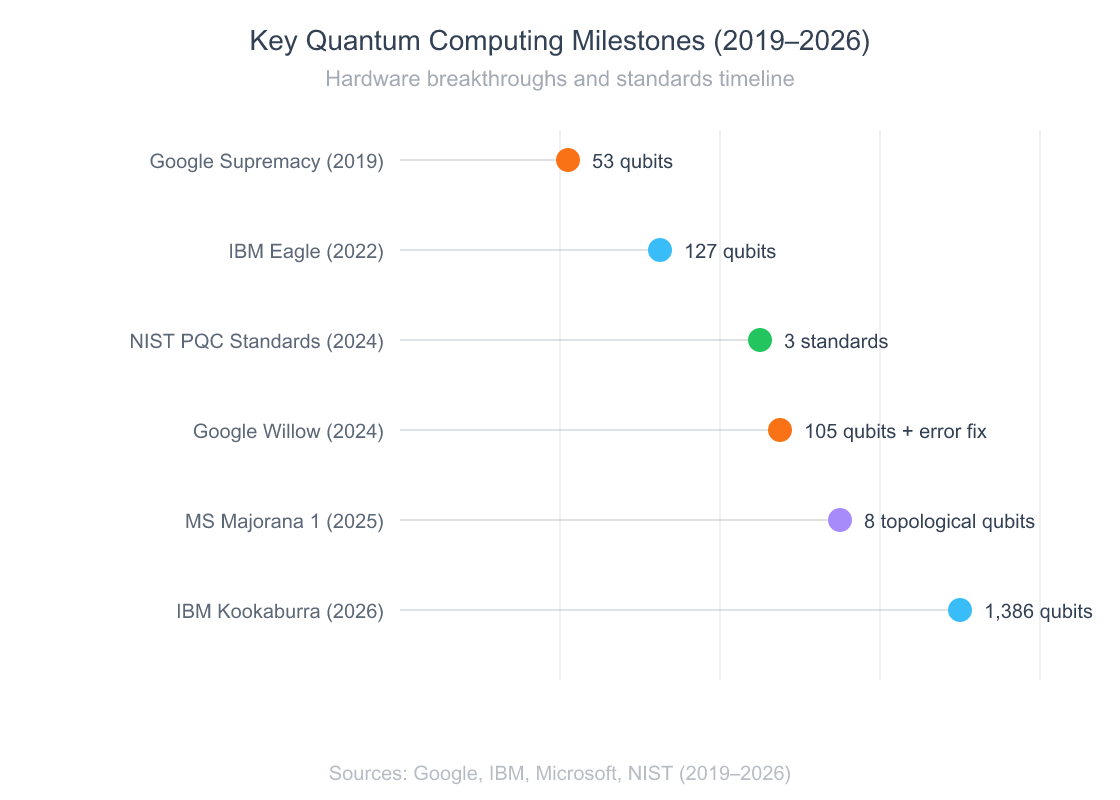
From 53 qubits in 2019 to 1,386 in 2026 — quantum hardware is advancing rapidly while post-quantum standards race to keep web security ahead of the threat.
FAQ
What is quantum computing, and why does it matter for web developers?
Quantum computing uses quantum mechanics to solve specific problem types exponentially faster than classical computers. For web developers, it matters because quantum computers will break RSA and ECC encryption — the algorithms protecting every HTTPS connection and digital signature. NIST will deprecate these algorithms by 2030 and disallow them by 2035 (NIST IR 8547, 2024).
When will quantum computers actually break encryption?
Current estimates place “Q-Day” around 2032, with roughly 1,000-1,400 logical qubits needed to factor RSA-2048 (Post-Quantum, 2025). But “harvest now, decrypt later” attacks are happening already, meaning data encrypted today could be decrypted retroactively. The timeline for concern isn’t Q-Day — it’s the retention period of your data.
Do I need to learn quantum programming to prepare?
No. Most web developers don’t need to write quantum algorithms. You need to understand the cryptographic threat, audit your dependencies for quantum-vulnerable algorithms (RSA, ECC, ECDSA), and migrate to NIST’s post-quantum standards (ML-KEM, ML-DSA). The tooling change is similar to upgrading from SHA-1 to SHA-2.
How much does it cost to experiment with quantum computing?
Free tiers exist on all major platforms. IBM Quantum provides free access to real quantum hardware and simulators. AWS Braket offers simulator access in its free tier and charges per-task for real hardware (typically $0.30-$0.75 per task). Azure Quantum provides credits for new users. You don’t need a budget to start learning.
What’s the difference between post-quantum cryptography and quantum cryptography?
Post-quantum cryptography (PQC) refers to classical algorithms designed to resist quantum attacks — these run on regular computers. Quantum cryptography uses quantum mechanics itself for secure communication (like quantum key distribution). Web developers should focus on PQC. It’s what NIST has standardized and what your TLS stack will adopt.
understanding modern cryptography
Is my web application already vulnerable to quantum attacks?
Not to direct decryption — yet. But if your application handles data that must stay confidential for 10+ years (medical records, financial data, government communications), it’s vulnerable to harvest-now-decrypt-later attacks today. Cloudflare reports that over 50% of human web traffic through its network already uses post-quantum key exchange (Cloudflare, 2025).
Should I wait for quantum computing to mature before acting?
No. The migration timeline is the constraint, not the quantum hardware timeline. It took 12+ years to migrate from SHA-1 to SHA-2. NIST’s 2035 deadline gives you less than a decade. Start with a cryptographic audit now, and test hybrid PQC in staging this year. The organizations that start early will avoid the scramble.
The Quantum Future Is a Security Migration
The most important takeaway for web developers: quantum computing’s first real impact on your work won’t be quantum algorithms or quantum speedups. It’ll be a cryptographic migration that touches every layer of your stack.
NIST has finalized the replacement standards. Browser vendors are shipping support. Cloudflare is already protecting majority traffic with hybrid post-quantum encryption. The question isn’t whether you’ll migrate — it’s whether you’ll do it proactively or in a scramble.
Quantum computing as a broader technology will take years to deliver on its optimization and simulation promises. McKinsey’s $72 billion by 2035 projection reflects real potential, but most of that value will accrue in pharma, finance, and materials science — not in typical web application development. For web developers, the actionable concern is narrower and more concrete: secure your stack against quantum threats now, and keep an eye on QaaS platforms for future opportunities.
The developers who act early won’t just protect their applications. They’ll build expertise that becomes increasingly valuable as every enterprise confronts this migration. Bain estimates it takes three to four years to go from awareness to a structured PQC approach (Bain & Company, 2025). Starting now is the strategic move.
Start with the audit. Test hybrid PQC. Update your dependencies. That’s the practical path forward.
preparing for technological shifts
Continue Learning
Fundamentals:
- Understanding API Security Layers
- Database Fundamentals Every Developer Should Know
Applied Topics:
- The Developer Job Market After AGI
- The Rise of AI-Native Apps
Infrastructure:
- Payment Gateway Security for Developers