How Do You Secure an API? The 4-Layer Framework That Actually Works
APIs are the backbone of every modern application — and the most common entry point for attackers. Most developers bolt security on as an afterthought: one middleware, one config flag, one if user.is_authenticated check. That’s not security. That’s a single lock on a door with three open windows.
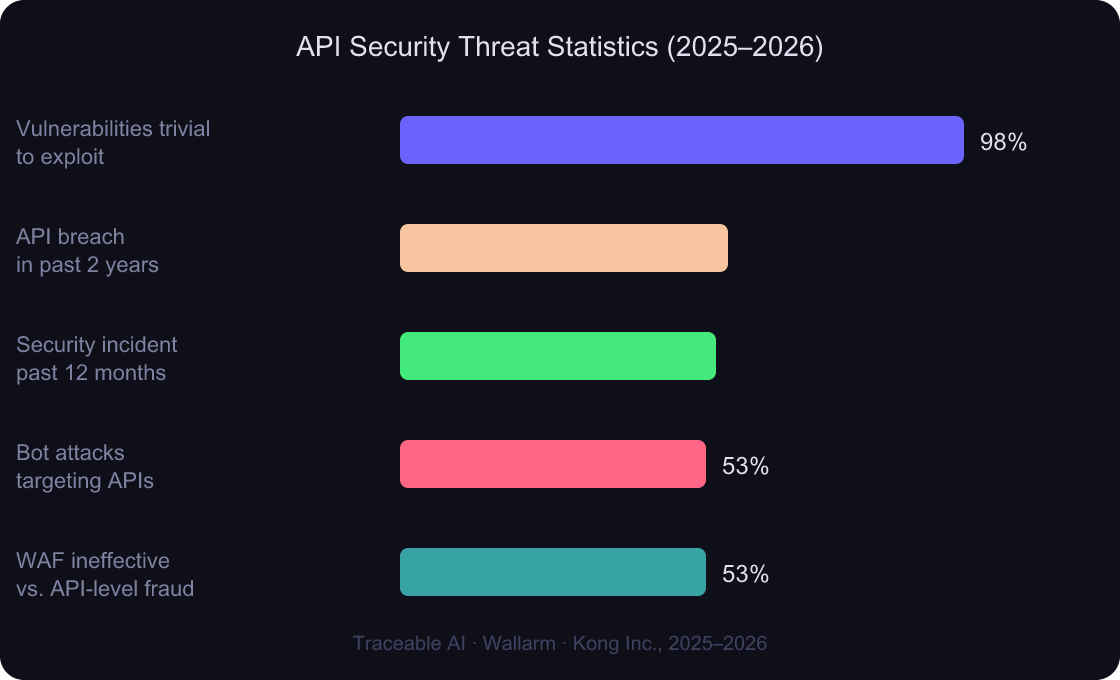
The correct mental model is layers. Each layer stops a different class of attack. Skip one, and the whole system fails. 57% of organizations experienced an API-related data breach in the past two years (Traceable AI, 2025). That number drops sharply when all four layers are in place.
This guide walks through each layer — what it stops, how it works, and the one rule that keeps you from getting it wrong.
REST API design fundamentals
TL;DR: API security requires four distinct layers: traffic control (rate limiting + WAF) to stop abuse, origin control (CORS + VPN) to restrict access points, request authenticity (CSRF tokens + JWT) to verify intent, and input/output safety (SQL/XSS prevention) to protect data. According to Traceable AI (2025), 53% of organizations have already faced bot attacks on their APIs — and a single missing layer is all it takes to get breached.
Why Do So Many APIs Get Breached?
98% of API vulnerabilities are classified as easy or trivial to exploit (Wallarm, 2026), and 59% require no authentication at all. These aren’t sophisticated zero-days. They’re basic misconfigurations that any developer could prevent — but most don’t know where to look first.
The root cause is almost always single-layer thinking. Teams implement OAuth, call it done, and leave rate limiting gaps wide open for brute-force attacks. Or they configure CORS and assume that covers cross-origin threats — not realizing CORS doesn’t touch server-to-server requests. Security fails at the seams between what you implemented and what you forgot.
What do the four layers actually look like in practice?
Sources: Traceable AI 2025 State of API Security, Wallarm 2026 API ThreatStats Report, Kong Inc. API Security Perspectives 2025
According to Wallarm’s 2026 API ThreatStats Report, 43% of all newly added CISA Known Exploited Vulnerabilities in 2025 were API-related — 106 of 245 total KEVs. The report also confirms that 98% of API vulnerabilities are easy or trivial to exploit and 59% require no authentication. This makes API hardening one of the highest-leverage security investments any engineering team can make.
OWASP API Security Top 10 explained
How Does Traffic Control Prevent API Abuse?
37% of all internet traffic consists of bad bots (Imperva, 2025) — and automated traffic now makes up 51% of all web requests for the first time in a decade. Traffic control is the first layer that stands between your API and that flood: brute-force login attempts, credential stuffing, scraping, and volumetric DDoS.
Rate Limiting
Rate limiting caps how many requests a client can send in a given time window. At its simplest: 100 requests per minute per IP. In practice, you need multiple scopes — per IP, per user account, and per API key — because one is never enough.
The rule worth memorizing: even authenticated users must be rate-limited. Authenticated ≠ trusted. A legitimate account can be compromised, scripted, or abused. Treat every token like it could be automated.
Common rate limit strategies:
- Fixed window — simple, but vulnerable to burst attacks at window boundaries
- Sliding window — smoother enforcement, eliminates the boundary exploit
- Token bucket — allows short bursts while enforcing a long-run average
In practice: Fixed-window limits at minute boundaries create a predictable attack surface. An attacker who knows your window resets at :00 can send 99 requests at :59 and 99 more at :00 — 198 requests in 2 seconds while staying under your limit. Sliding window eliminates this completely. It’s worth the slightly higher implementation cost.
Web Application Firewall (WAF)
A WAF inspects incoming requests and blocks patterns matching known attack signatures — SQL strings in query params, oversized headers, malformed JSON. It operates at the edge, before your application code runs.
Here’s the problem: 53% of organizations report their WAF or WAAP is ineffective at detecting API-level fraud (Traceable AI, 2025). WAFs were designed for HTML web apps. A WAF blocking <script> tags in form fields won’t catch {"query": "1=1 OR"} in a POST body unless you’ve explicitly configured it for JSON traffic.
Use a WAF — but configure it for your API’s actual request shape. Set rules for JSON payloads, not just URL parameters. And pair it with rate limiting; WAFs filter, they don’t throttle.
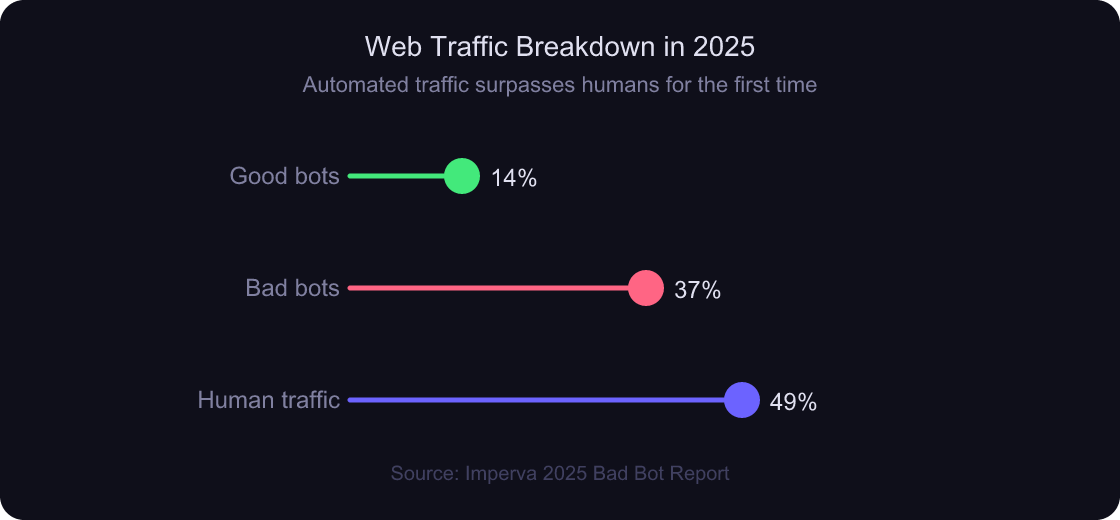
Source: Imperva 2025 Bad Bot Report — Automated traffic (51%) now exceeds human traffic for the first time in a decade
According to Imperva’s 2025 Bad Bot Report, 37% of all internet traffic now consists of bad bots, with total automated traffic surpassing human activity at 51% — a first in a decade. For API teams, this means that without rate limiting, a significant portion of your inbound traffic is abuse by default, not by exception.
sliding window rate limiting implementation
CORS vs VPN: What’s the Real Difference for API Access Control?
CORS and VPN sound like they solve the same problem — “who can access my API?” — but they operate at completely different layers and protect against completely different threats. Confusing them is one of the most common API security mistakes, and it’s more dangerous than it looks.
CORS (Cross-Origin Resource Sharing)
CORS is a browser-enforced mechanism. It tells the browser whether a web page at app.example.com is allowed to make requests to api.example.com. The browser sends a preflight OPTIONS request; your API responds with headers listing allowed origins; the browser decides whether to allow the main request.
The critical limitation: CORS is not an authentication mechanism. It controls which browser-based origins can talk to your API — nothing more. Server-to-server calls, curl, Postman, and every non-browser HTTP client completely bypass CORS. An attacker doesn’t need a browser. CORS stops malicious cross-origin browser scripts; it does nothing to stop a determined attacker with a terminal.
The correct CORS posture: set the minimum necessary origin list. Access-Control-Allow-Origin: * on a private API is almost always wrong. Lock it to specific production domains.
VPN and Private Network APIs
VPN and private network controls are the network-level answer to origin control. Internal APIs — billing, admin, user management — shouldn’t be publicly routable at all. VPN puts them behind a network boundary that no browser-origin header can bypass. Only authenticated network clients can even reach the TCP port.
Zero-trust is replacing traditional VPN for many teams: instead of “authenticated to the network = trusted,” each API call must present its own credential regardless of network position. This is strictly more secure and fits modern cloud deployments better.
Worth noting: Many teams treat CORS misconfiguration as a low-severity finding because “the attacker would need a browser.” That’s backwards. CORS is your only control against malicious browser-based attacks (like XHR from a phishing page). If
Access-Control-Allow-Origin: *is set on an endpoint that reads session cookies, it’s a critical vulnerability — the browser will happily attach cookies and forward the response to the attacker’s origin.
CORS is enforced by browsers and controls which web origins can issue cross-origin requests — it does nothing to prevent server-to-server abuse or curl-based attacks. VPN and network-level access controls protect APIs at the infrastructure layer, completely independent of browser behavior. Using both isn’t redundant; they address different attack vectors entirely. Neither substitutes for the other.
zero-trust network architecture
How Do CSRF Tokens and JWT Protect Against Forged Requests?
The goal of request authenticity is to prove not just who is making a request, but that the request was intentionally initiated by a legitimate user. Both CSRF tokens and JWT serve this purpose — but they apply to different auth models, and mixing them up creates security gaps.
CSRF Tokens (For Cookie-Based Auth)
Cross-Site Request Forgery tricks a logged-in user’s browser into making unintended requests to your API. Because browsers automatically send cookies with every request to a matching domain, a malicious page can trigger account changes or fund transfers without the user knowing.
CSRF tokens break this by requiring a secret value the malicious site can’t know. The server issues a token per session; the client includes it in every state-changing request; the server validates it before acting. No token match = request rejected.
When do you need CSRF tokens? Only when your API uses cookie-based session authentication. If your API uses Authorization: Bearer <token> headers and doesn’t touch cookies, CSRF isn’t a threat — browsers don’t automatically send custom headers cross-origin.
JWT and OAuth (For Token-Based Auth)
JWT (JSON Web Token) is the standard for stateless API authentication. The server signs a token containing the user’s identity and permissions; clients include it in the Authorization header; the server validates the signature without a database lookup.
85% of enterprises use OAuth to secure external application integrations (Ping Identity, 2025). OAuth builds on JWT by adding a delegation model — users grant third-party apps access to specific resources without sharing credentials. The access token has a short lifetime; the refresh token handles renewal.
The rule of thumb: CSRF → cookies → need CSRF tokens. JWT → headers → no CSRF risk. Protecting a JWT API with CSRF tokens adds complexity without security benefit.
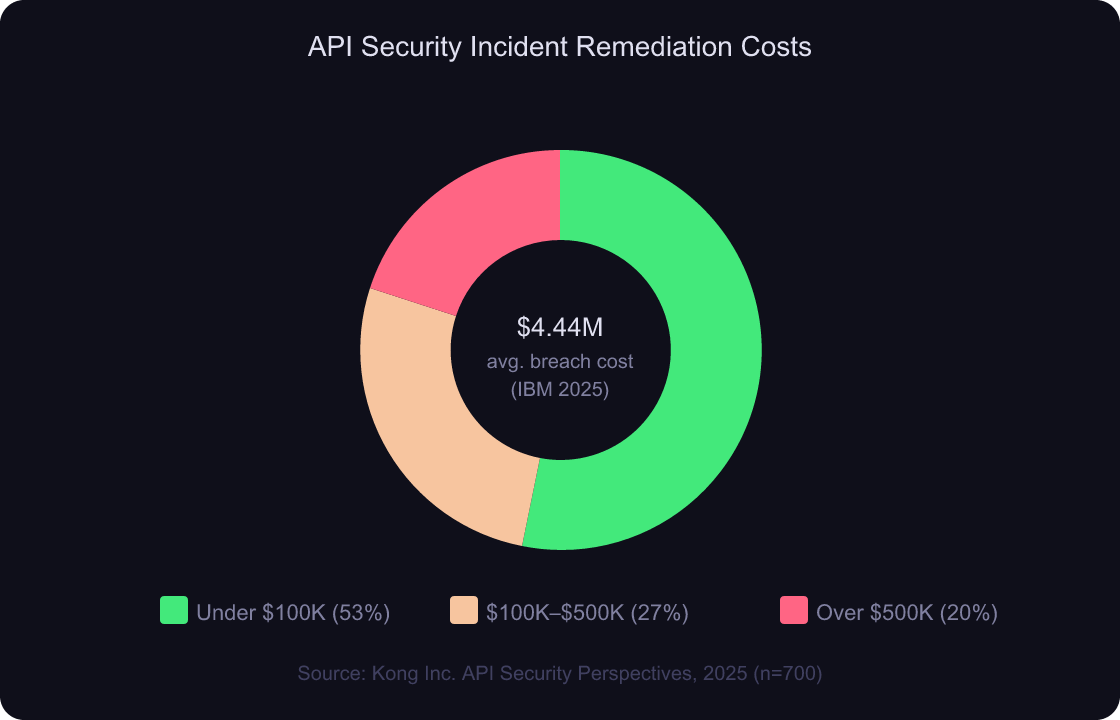
Source: Kong Inc. API Security Perspectives 2025 — 47% of breached organizations faced remediation costs over $100,000
Kong Inc.’s 2025 API Security Perspectives survey (n=700 IT leaders) found that 55% of organizations experienced an API security incident in the past 12 months, with one-third classified as “severe.” Of those breached, 47% faced remediation costs over $100,000. The financial case for correctly implementing JWT and CSRF protections is clear: the cost of a breach far exceeds the cost of proper authentication design.
JWT security best practices
How Do SQL Injection and XSS Attacks Exploit APIs?
The final layer protects the data flowing in and out of your API. SQL injection and XSS don’t exploit misconfigured headers or missing tokens — they exploit the content of requests your application trusts and processes. The golden rule: never trust user input. Ever.
SQL Injection
SQL injection happens when user-controlled data is interpolated directly into a database query. The classic example: SELECT * FROM users WHERE email = '${input}' — if input is admin@site.com' OR '1'='1, the query returns every user in the database.
The fix is parameterized queries (prepared statements), not sanitization. Sanitization is fragile — you’ll miss edge cases. Parameterized queries separate data from code at the database driver level, making injection structurally impossible regardless of input content.
Over 20% of closed-source projects show SQL injection vulnerabilities on initial security assessment (Aikido, 2024–2025), with affected codebases averaging 30 vulnerable locations. NoSQL databases aren’t immune either — MongoDB’s $where operator and similar vectors allow analogous attacks if inputs aren’t validated before being passed into query objects.
XSS (Cross-Site Scripting)
XSS targets your users by injecting malicious scripts into API responses rendered by browsers. Stored XSS is the most dangerous: an attacker submits a script via your API that gets saved to your database and served to every user who views that resource. Reflected XSS bounces the script off a single response without persistence.
XSS has generated over 30,000 CVEs — more than twice the 14,000+ from SQL injection (OWASP, 2025). In API contexts, XSS often targets JSON responses rendered by front-end frameworks without proper escaping.
The fix: HTML-encode all output, use Content-Security-Policy headers to restrict script execution, and treat every piece of user data as untrusted — even content retrieved from your own database, because your database might already be poisoned.
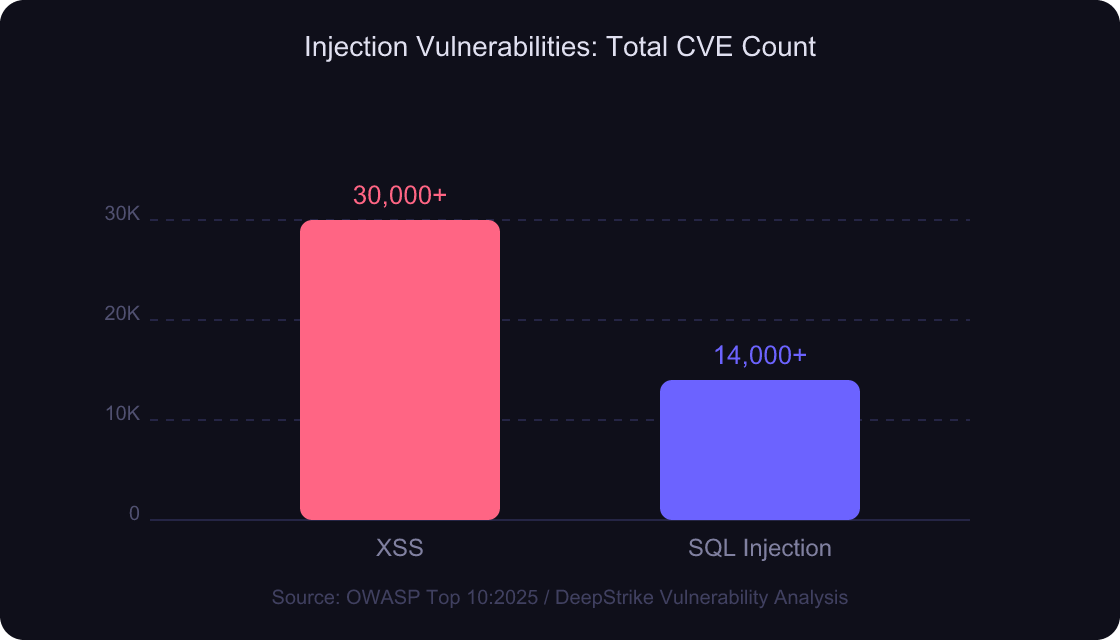
Source: OWASP Top 10:2025 — XSS has generated over 30,000 CVEs, more than twice the count for SQL injection
Worth noting: Most SQL injection guidance focuses on
SELECTandWHEREclauses in relational databases. GraphQL APIs introduce a different injection vector: deeply nested queries that trigger unintended joins or bypass field-level authorization. The parameterized query habit doesn’t automatically transfer — GraphQL resolvers need their own input validation layer, and most WAFs have no GraphQL-aware rules at all.
XSS has generated over 30,000 CVEs and SQL injection over 14,000, with injection ranked #5 in OWASP’s Top 10:2025 and present in 100% of applications tested for some form of it (OWASP, 2025). For APIs specifically, stored XSS via JSON responses and NoSQL injection through MongoDB’s $where operator represent fast-growing attack surfaces that traditional WAF rules don’t cover.
parameterized queries vs ORM
The API Security Checklist: All 4 Layers Together
Security is only as strong as its weakest layer. Here’s a practical checklist — verify your API covers all four before it ships:
Layer 1 — Traffic Control
- [ ] Rate limiting applied per IP, per user account, and per API key (sliding window preferred)
- [ ] WAF configured for JSON/API request shapes, not just HTML form inputs
- [ ] DDoS mitigation at the edge (CDN or cloud provider level)
Layer 2 — Origin & Access Control
- [ ]
Access-Control-Allow-Originset to explicit domains — never*for private APIs - [ ] Internal APIs behind VPN or private network, not publicly routable
- [ ]
SameSite=StrictorSameSite=Laxon all session cookies
Layer 3 — Request Authenticity
- [ ] CSRF tokens on all state-changing endpoints if using cookie auth
- [ ] JWT with short expiry (15–60 min) + refresh token rotation
- [ ] OAuth scopes as narrow as possible — principle of least privilege
Layer 4 — Input & Output Safety
- [ ] All database queries use parameterized statements (zero string interpolation)
- [ ] All user-supplied content HTML-encoded before rendering
- [ ]
Content-Security-Policyheader restricts inline script execution
API security audit checklist
Frequently Asked Questions
What’s the difference between authentication and authorization in API security?
Authentication proves who you are (valid JWT, correct password). Authorization determines what you’re allowed to do (can this user delete this resource?). Both are required, but neither substitutes for the other. 59% of exploitable API vulnerabilities require no authentication at all (Wallarm, 2026), making authentication the highest-priority layer to get right first.
Should I use CSRF tokens if my API uses JWT bearer tokens?
No. CSRF attacks exploit automatic cookie-sending by browsers. If your API uses Authorization: Bearer headers, browsers don’t auto-attach those cross-origin — CSRF isn’t a threat. CSRF tokens are specifically for cookie-session APIs. Adding them to JWT APIs introduces complexity without any security benefit.
How do I rate-limit API endpoints without blocking legitimate users?
Use per-user rate limits (not just per-IP) so shared IPs — corporate NAT, mobile carriers — don’t block legitimate users. Implement graduated responses: throttle first (add delay), then 429 Too Many Requests, then temporary block. Always expose rate limit headers (X-RateLimit-Remaining, Retry-After) so clients can back off gracefully.
rate limit response headers
What’s the fastest SQL injection fix for an existing codebase?
Replace all string-interpolated queries with parameterized queries. In most languages: db.query("SELECT * FROM users WHERE id = ?", [userId]) instead of "SELECT * FROM users WHERE id = " + userId. If you use an ORM, verify it uses parameterized queries by default — most do, but raw query methods often don’t.
Is NoSQL safe from injection attacks?
No. MongoDB’s $where, $regex, and operator injection attacks are the NoSQL equivalent of SQL injection. If your API passes user input directly into a MongoDB query object without validation, an attacker can send {"$gt": ""} to bypass field comparisons entirely. Validate the shape and type of all input — never assume a non-relational database is injection-proof.
Conclusion
API security isn’t a feature you ship once — it’s a property you maintain across four distinct layers. Each layer stops attacks the others can’t touch. Rate limiting and WAF can’t stop an XSS attack. CORS can’t stop SQL injection. JWT can’t stop a brute-force bot if there’s no rate limit. The layers are additive, not interchangeable.
Start with the layer your current architecture is most obviously missing. Add rate limiting first if you have nothing — it stops the widest range of automated abuse with the least implementation complexity. Then work through access control, request authenticity, and input safety in order.
Key takeaways:
- Even authenticated users must be rate-limited
- CORS is not authentication — it’s browser-level origin filtering
- CSRF tokens are for cookie auth; JWT covers token-based auth
- Never trust user input — parameterize everything, encode all output
HTTPS and TLS configuration guide